本文主要介绍谷歌云对象存储攻防的方式
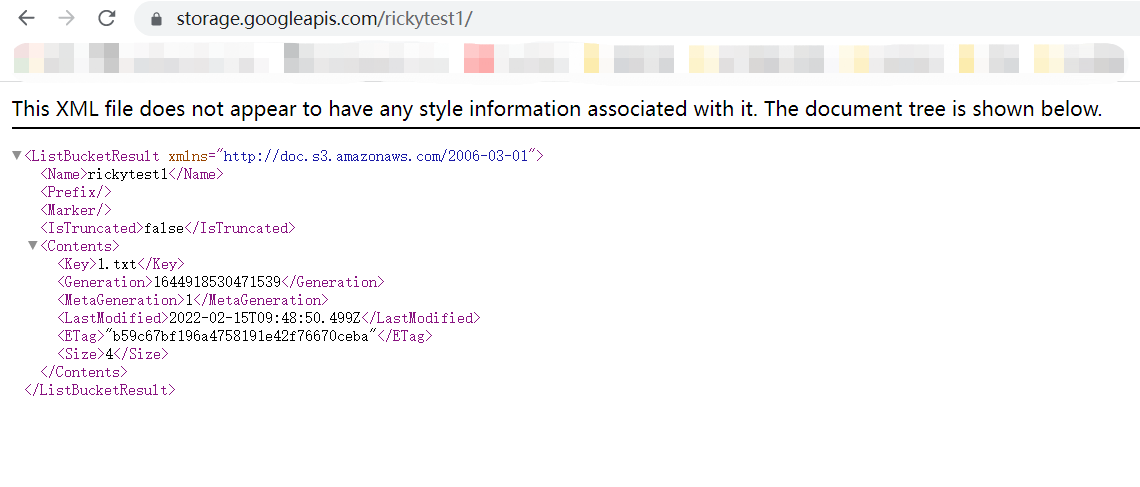
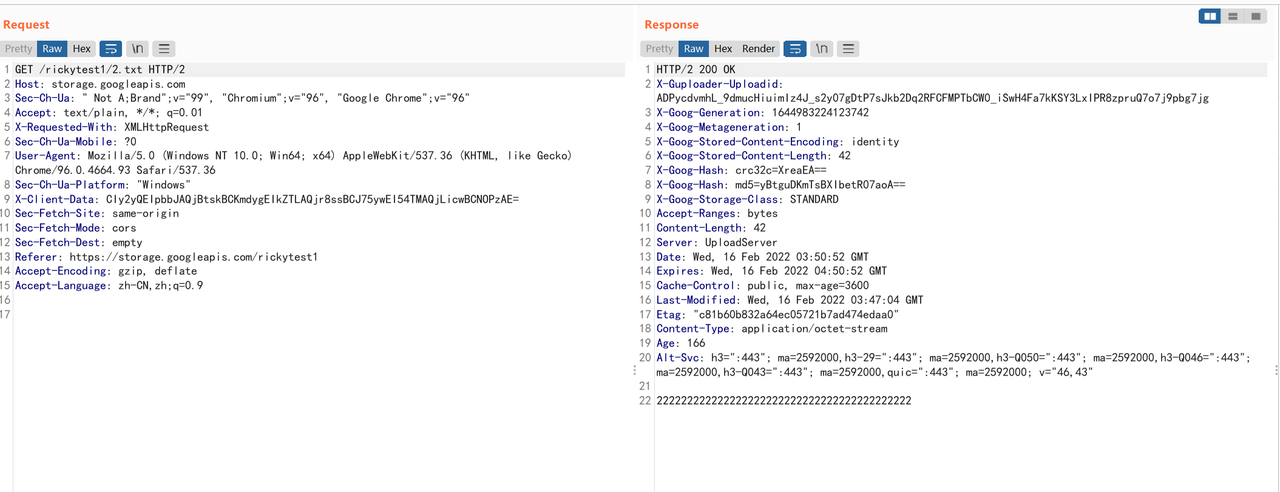
1、存储桶配置错误-公开访问

当创建的存储桶配置了allUsers拥有GCS对象的读取权限时,该存储桶可以被任何用户公开访问
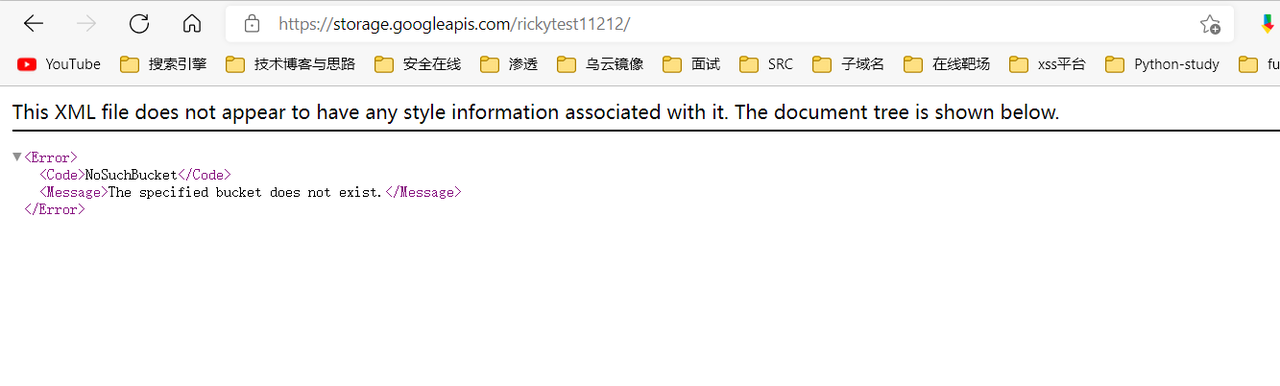
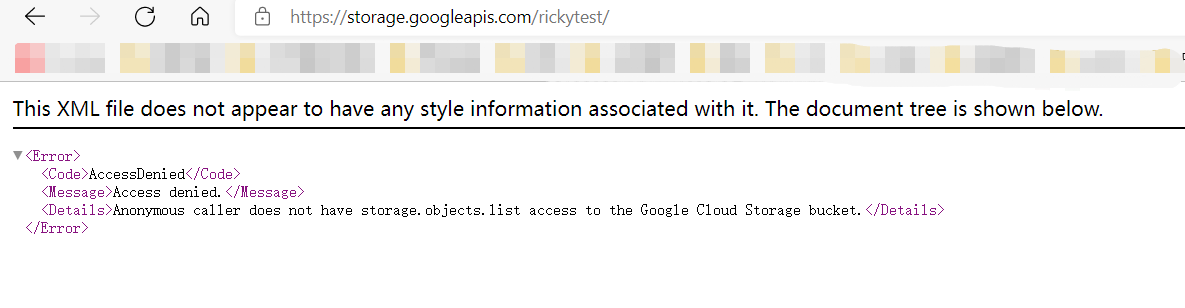
2、Bucket爆破
当不存在时访问会提示NoSuchBucket
当存在时会出在下面情况,公开访问和拒绝访问

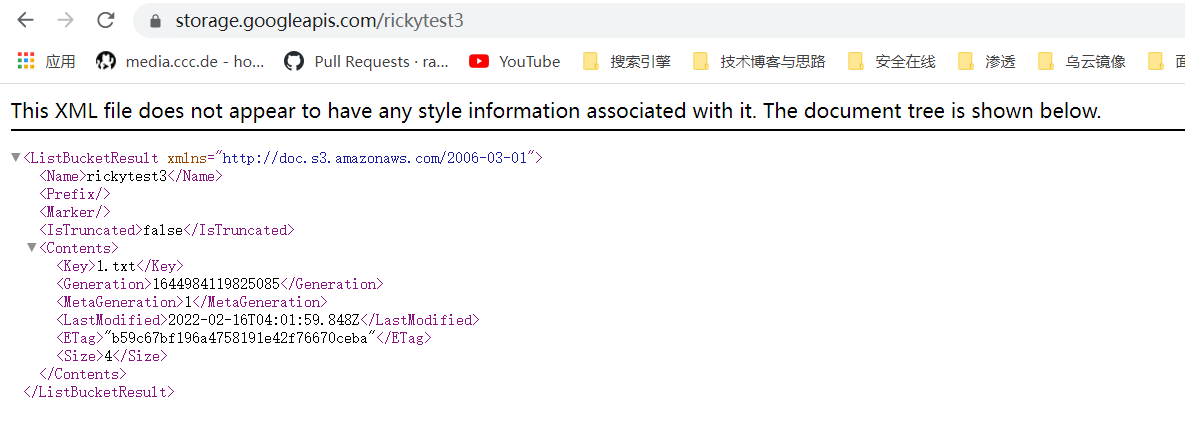
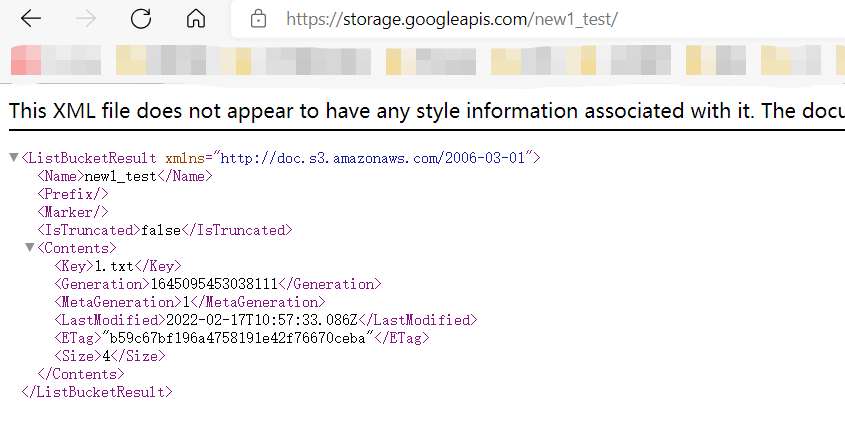
3、Bucket Object 遍历
当对allUsers配置了Storage Object Viewer 或者Storage Legacy Bucket Reader权限时就会将存储桶内容遍历出来并且可以读文件内容
4、任意文件上传和覆盖
当存储桶配置了allUsers拥有 Storage Legacy Bucket Owner、Storage Object Admin或者Storage Legacy Bucket Writer 权限时,任何用户都可以上传任意文件到存储桶并覆盖已经存在的文件

5、SERVICE ACCOUNT泄漏
- Github代码中泄露
- 网站JS代码

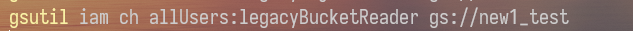
6、Bucket IAM 策略可写
访问权限控制为统一时,对象访问权限完全由存储桶级权限 (IAM) 进行控制
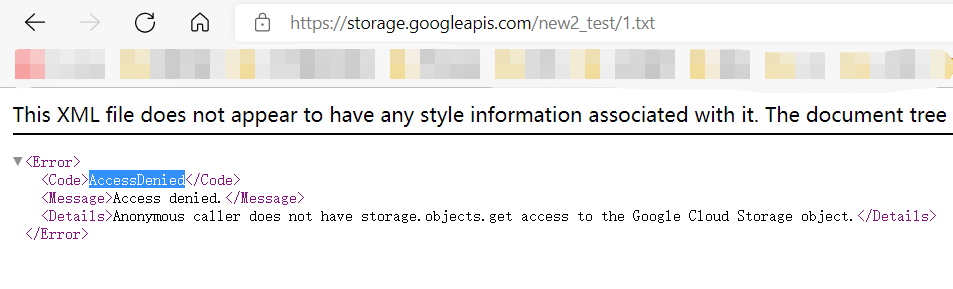
直接访问存储桶发现AccessDenied
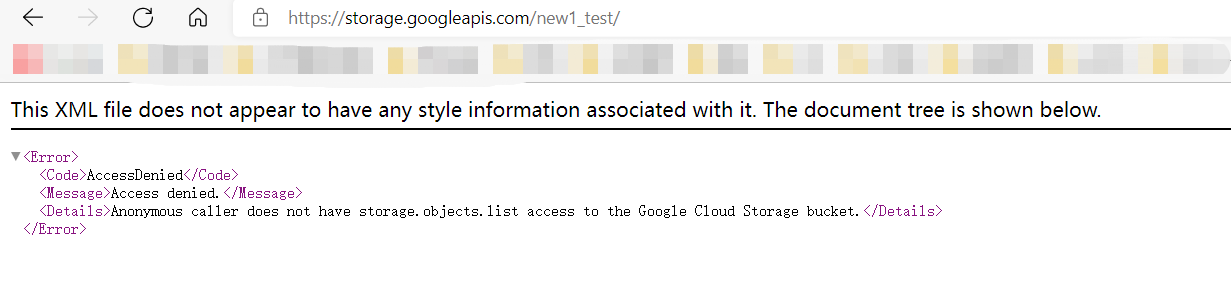
查看Bucket IAM策略

上图标识部分表示所有的谷歌认证用户都有权有权获取和设置任意 IAM 策略,通过gsutil去修改IAM策略
再次去访问存储桶
7、Object ACL可写
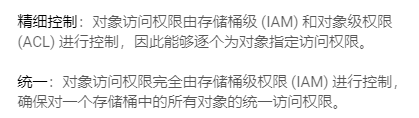
访问存储桶对象时提示AccessDenied
当访问权限控制为精细控制时,查看Object ACL,发现所有谷歌认证用户都能修改Object ACL
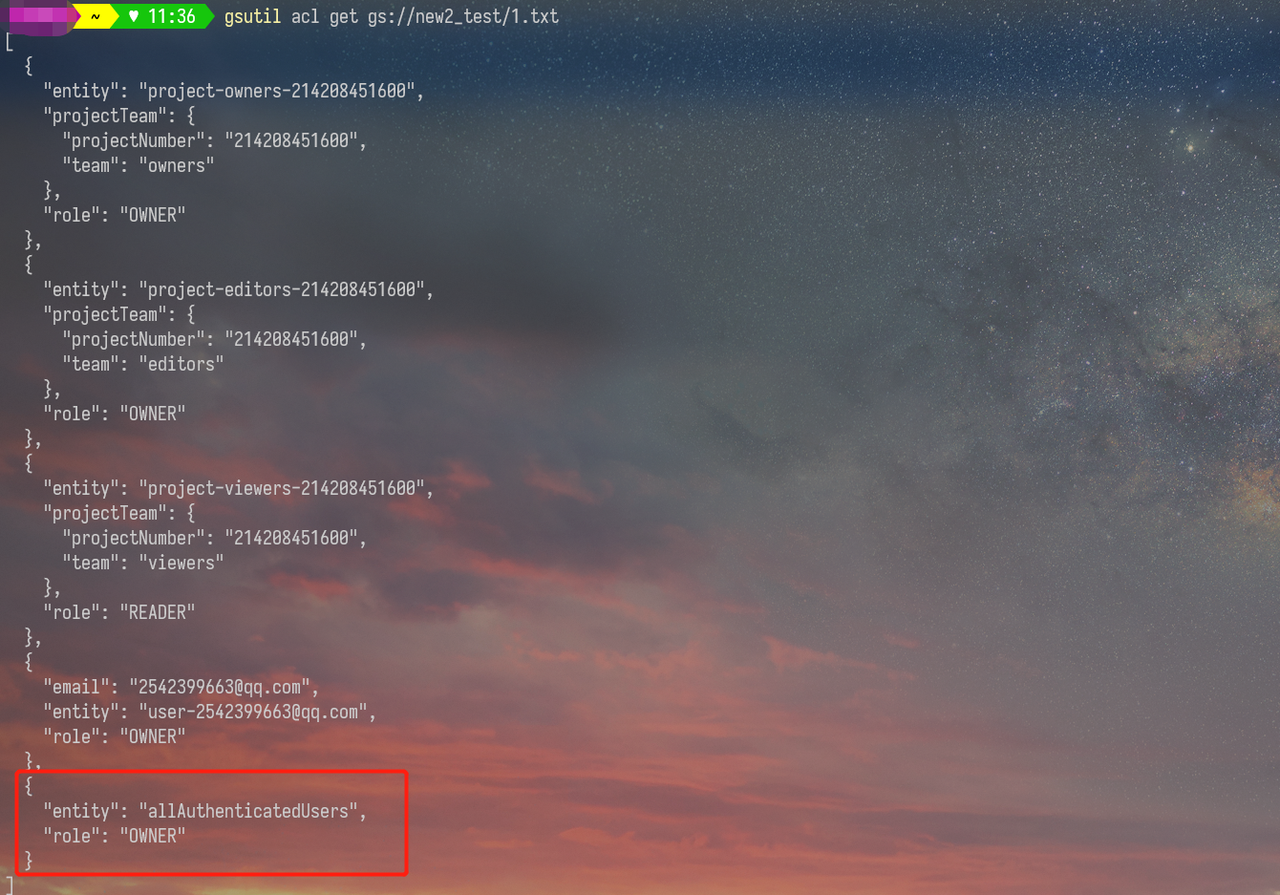
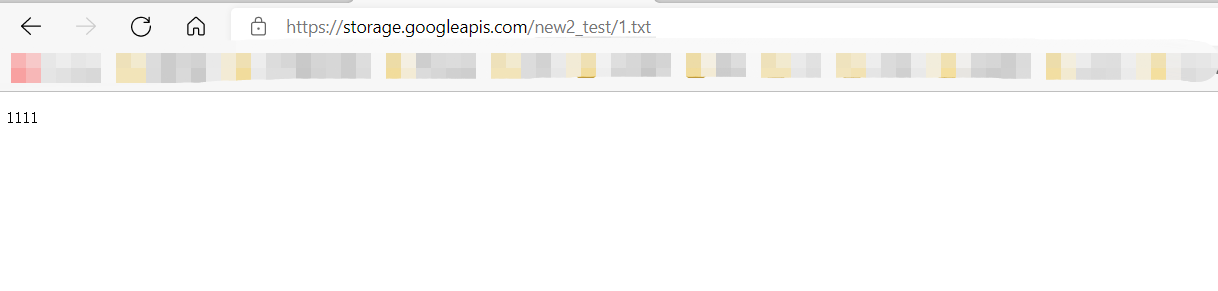
gsutil acl ch -u allUsers:R gs://new2_test/1.txt
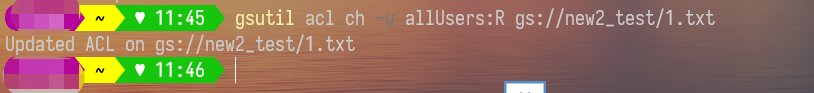
修改ACL后任何用户都可以访问
六大云存储攻击文章:
阿里云 OSS对象存储攻防(UzJu):https://zone.huoxian.cn/d/918-oss
Aws S3 对象存储攻防(TeamsSix):https://zone.huoxian.cn/d/907-aws-s3